securing your server is one of the most important things you need to do when you’re setting up a server.
Start Using a Firewall
It’s important to note that if a firewall is incorrectly configured, it can block desired traffic.
On Fedora, CentOS, Red Hat, and similar distributions, the firewall software installed by default is firewalld, which is configured and controlled with the firewall-cmd command. On Debian and most other distributions, firewalld is available to install from your software repository.
#centos
sudo yum install firewalld
----------------------------
ubuntu
#sudo apt install firewalldUse Secure Shell(SSH)
SSH is a secure protocol that use encryption technology during communication with server.
#vi /etc/ssh/sshd_config
---------------
#PermitRootLogin no
#Protocol 2cPanel Security
Many of our Technical Support Analysts recommend that you use CSF (ConfigServer Firewall), a free product that ConfigServer provides. csf uses a set of predefined rules to determine whether the data it should be allowed to pass or be blocked.
To install CSF, perform the following commands:
cd /usr/src
rm -fv csf.tgz
wget https://download.configserver.com/csf.tgz
tar -xzf csf.tgz
cd csf
sh install.shsymlink vulnerability
This vulnerability allows a malicious user to change a symlink multiple times during the interval between when Apache checks for a file’s presence and creates the file. This action allows the malicious user to inject malicious content that links to a user-owned file.
You can turn on symlink protection (WHM >> Home >> Service Configuration >> Apache Configuration >> Global Configuration) allows you to configure various Apache options that reside in the root (/) directory. also The SymLinksIfOwnerMatch option exposes Apache to a race condition through symlinks.
Update the kernel
To update you kernel, perform the following commands:
yum -y update kernelModSecurity
modsecurity is a open-source web-based firewall application (or WAF) that configured to protect web applications from various attacks. ModSecurity supports flexible rule engine to perform both simple and complex operations
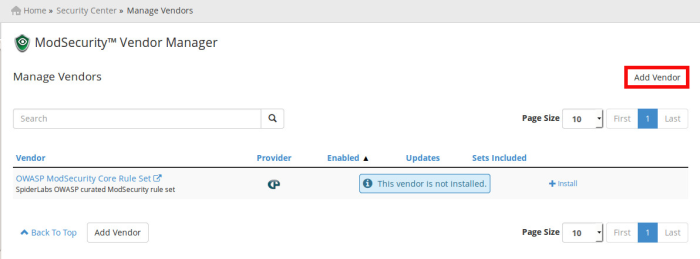
in cpanel ,The ModSecurity Vendors interface allows you to install and manage your ModSecurity vendors.
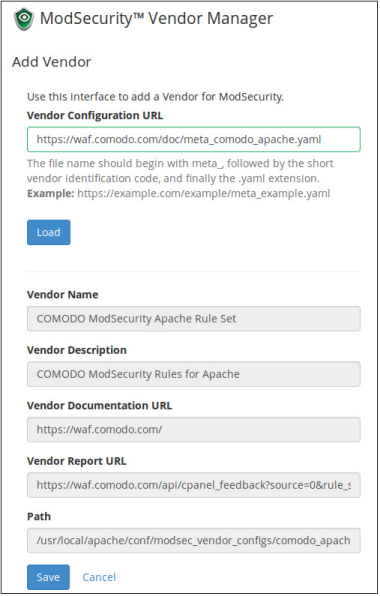
To add a ModSecurity vendor, perform the following steps:
- Click Add Vendor.
- In the Vendor Configuration URL text box, enter the URL for the ModSecurity vendor.
- Click Load. The Vendor Name, Vendor Description, Vendor Documentation URL, and Vendor Path text boxes automatically load vendor data.
- After you confirm that the vendor data is correct, click Save.
In the ‘Add Vendor’ page, enter the vendor configuration URL depending on your web server type.
#Comodo ModSecurity Apache Rule Set
https://waf.comodo.com/doc/meta_comodo_apache.yaml
#Comodo ModSecurity LiteSpeed Rule Set https://waf.comodo.com/doc/meta_comodo_litespeed.yaml